未发布 集成的HTTP嗅探器HttpWatch更新至v11.0.21,改进F5刷新机制 HttpWatch是一款集成的HTTP嗅探器,为IE和Firefox提供新的方法以查看您网站的负载和运行情况。你可以直接在浏览器中调试由web页面生成的网络流量,而无需切换到一个单独的工具。
2017慧都十四周年狂欢搞事情!砸金蛋100%抽现金红包、满额豪送iPhone X、iPhone 8、DevExpress汉化免费送、团队升级培训套包劲省10万元......更多惊喜等您来探索!

未发布 GIS软件开发工具包TatukGIS Developer Kernel更新至v11.9丨附下载 GIS定制开发首选控件,帮您轻松搞定高效、优质、实惠的GIS解决方案
TatukGIS Developer Kernel(DK)是一个用于开发自定义地理信息系统(GIS)应用程序以及解决方案的综合性软件开发工具包(SDK)。众所周知,构建一个庞大的地理信息系统需要花费大量的金钱和人力,而TatukGIS却是同类产品中性价比最高的控件,TatukGIS Developer Kernel DK因其功能强大,价格适中,已被超过 50个国家的个人、公司、以及政府等客户用来实现其地理信息系统解决方案。根据不同地首选开发环境,本产品分别以五个独立产品的形式提供(即VCL、.NET/WPF、ActiveX、Compact Framework和ASP.NET),各个产品使用相同的框架、应用程序编程接口(API)技术。
TatukGIS Developer Kernel v11.9更新内容
改进:
Legend控件的初始版本。其余的功能是完整的。DK-9660
坐标系统定义匹配EPSG 9.2,也支持GD2020。 DK-9769 DK-9664
Scale和Nort Arrow控件的发光阴影。DK-9755
添加Antenna、Tower Communication、Wind Turbine符号。 DK-9725 DK-9711
大大改进了DXF。DK-9719
改进FMX桌面的触摸手势。DK-9747
VCL添加pinch和pans手势。DK-7462
支持最初的Java Legend控件。
修复其他问题。
2017慧都十四周年狂欢搞事情!砸金蛋100%抽现金红包、满额豪送iPhone X、iPhone 8、DevExpress汉化免费送、团队升级培训套包劲省10万元......更多惊喜等您来探索!

【示例教程】LEADTOOLS中如何通过OCR识别获取每一行文本 LEADTOOLS可帮您开发出功能强大的文档图像应用程序。其主要功能包括综合图像注释,专业的黑白图像显示(例如灰度级和偏黑),以及专业的黑白图像处理。其它功能包括对黑白图像的性能和内存进行优化,文档图像清理(包括倒置文本,去边界,去打孔机和去线)以及使用LEADTOOLS Fast TWAIN和WIA进行扫描。
本篇文介绍如何通过OCR分别识别获取文档的每一行文本。有一种方法类似于我们的IOcrZoneCharacters.GetWords方法可检索文档的每一行。OCR引擎识别的每个字符都有一个位置。我们可以通过OcrCharacter 结构的position 属性访问这个位置。返回一个或多个OcrCharacterPosition 枚举成员:
下面写了一个简单的小例子,用OcrCharacterPosition 来分别识别出每一行的文字。
using (RasterCodecs codecs = new RasterCodecs())
{
codecs.Options.RasterizeDocument.Load.XResolution = 300;
codecs.Options.RasterizeDocument.Load.YResolution = 300;
RasterImage image = codecs.Load(inputFile);
using (IOcrEngine ocrEngine = OcrEngineManager.CreateEngine(OcrEngineType.Professional, false))
{
ocrEngine.Startup(null, null, null, @"C:\LEADTOOLS 19\Bin\Common\OcrProfessionalRuntime64");
using (IOcrDocument document = ocrEngine.DocumentManager.CreateDocument())
{
document.Pages.AddPage(image, null);
document.Pages[0].Recognize(null);
IOcrPageCharacters pageCharacters = document.Pages[0].GetRecognizedCharacters();
for (int i = 0; i < document.Pages[0].Zones.Count; i++)
{
IOcrZoneCharacters zoneCharacters = pageCharacters.FindZoneCharacters(i);
if (zoneCharacters != null)
{
foreach (var ocrCharacter in zoneCharacters)
{
OcrCharacterPosition position;
position = ocrCharacter.Position;
if ((position & OcrCharacterPosition.EndOfLine) == OcrCharacterPosition.EndOfLine)
{
Console.Write(ocrCharacter.Code + "\n");
}
else
{
Console.Write(ocrCharacter.Code);
}
}
}
}
}
}
}
2017慧都十四周年狂欢搞事情!砸金蛋100%抽现金红包、满额豪送iPhone X、iPhone 8、DevExpress汉化免费送、团队升级培训套包劲省10万元......更多惊喜等您来探索!

未发布 【百厂约惠】盘点2017年5款最好用的图形图像/CAD工具 图像已经成为网络不可或缺的一部分,相比文字来说图像更直观。那么各种图形图像的处理软件、控件就必不可少了。
今天为大家推荐慧都2017年5款最受欢迎的图形图像/CAD工具,附带各个软件、控件的基本介绍以及最新版本的下载地址,有兴趣的朋友可以免费下载进行试用。在使用过程中出现了任何问题,请联系我们的
在线客服。
Dynamic Web TWAIN是一个专为Web应用程序设计的TWAIN扫描识别控件。你只需在TWAIN接口写几行代码,就可以用兼容TWAIN的扫描仪扫描文档或从数码相机/采集卡中获取图像。然后用户可以编辑图像并将图像保存为多种格式,用户可保存图像到远程数据库或者SharePoint。这个TWAIN控件还支持上传和处理本地图像。
VectorDraw Developer Framework(VDF)是一个用于应用程序可视化的图形引擎库。有了VDF提供的功能,您可以轻松地创建、编辑、管理、输出、输入和打印2D和3D图形文件。该库还支持许多矢量和栅格输入和输出格式,包括本地PDF和SVG导出。
CAD .NET是一款在CAD领域被广泛应用的控件,可以快速准确的阅读DWG和DXF文件,并且通过Windows GDI+方法绘制件,支持多种文件格式,包括DWG、DXF、Gerber、光栅图像等,并支持部分编辑功能。
【CAD .NET最新版下载】
ImageGear for .NET是一款图形图像处理控件,具有扫描,压缩,浏览、添加注释,打印,图像编辑,OCR以及PDF和矢量图像支持,使开发人员可以快速地开发出图像处理程序,可用于.NET Framework2.0、3.0、3.5、4.0,ASP.NET,WPF,SilverLight,DirectX 10和Direct3D 10。支持超过100种图片格式,包含:TIFF, JPEG, CAD, Vector, 3D PDF, PDF/A, PS等。
【ImageGear for .NET最新版下载】
使用LEADTOOLS Document Imaging可帮您开发出功能强大的文档图像应用程序。其主要功能包括综合图像注释,专业的黑白图像显示(例如灰度级和偏黑),以及专业的黑白图像处理。其它功能包括对黑白图像的性能和内存进行优化,文档图像清理(包括倒置文本,去边界,去打孔机和去线)以及使用LEADTOOLS Fast TWAIN和WIA进行扫描。
【LEADTOOLS v19总套包免费下载】
郑重承诺:慧都所售产品均为厂商授权的正版产品,请完全放心!
*本活动最终解释权归慧都科技所有
咨询热线: 400-700-1020(免费) 023-66090381

未发布 屏幕录制软件ALLCapture常见问题合集(上) ALLCapture是一款实时抓取桌面的屏幕录制软件。实时、快速、轻松地录制屏幕,创建自己的屏幕录像、示例、指南、软件模拟以及无需任何编程的网络视频。制作步骤如此简单:录制-编辑-导出-播放。 使用ALLCapture遇到了问题?我们的FAQ将帮助你找到答案。
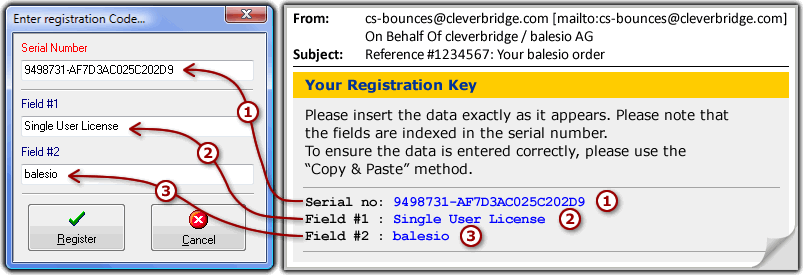
1、我的序列号和注册信息都无法使用?
注册信息包括三部分:“序列号”,“字段 #1”以及“字段 #2”-要成功注册你的软件这些信息都是必须。为了确保你的注册没有任何问题,请从发送给你的邮件中复制注册信息,然后粘贴到相应的注册字段。请参考以下截图。
2、ALLCapture对系统的最低要求是?
| 功能 | 要求 |
| 主要功能 | Windows 98或更高
最低1.2GHzPentium或兼容CPU
256MB内存
50MB可用硬盘
SVGA显卡,256色 |
| 对电影或视图截图 | Windows 2000或更高(文件格式为NTFS)
最低2GHz Pentium或兼容CPU
1GB内存
30GB可用硬盘
专业版SVGA显卡,最低显存256MB
(非集成显卡) |
3、最大帧速非常慢,我该怎么办?
当ALLCapture显示的帧速小于10FPS(帧每秒)时,要么是显卡不支持要么是驱动过期。用户可用升级电脑的显卡驱动来增加帧速,但是显卡或显卡芯片仍然无法支持。在购买新显卡前我们还是建议先升级显卡驱动。如果驱动升级成功,你可以在ALLCapture中新建一个项目,然后在“录制选项”页中点击“帧速”,然后再点击“刷新帧速最大值”按钮。
4、为什么录制的视频是黑色的一片?
先了解一下处理机制,电影是直接从显卡解码而来,这就是造成黑色一片的原因。Windows只能同时让一个屏幕可用,这样操作系统无法获取在屏幕下面的东西,因此ALLCapture也无法捕捉到。
用户可以通过停用显卡的硬件加速来捕获画面。硬件加速可以从这里找到:“开始>设置>控制面板>显示>设置>高级>疑难解答”,滑动控制条到“没有硬件加速”。
5、为什么ALLCapture没有录制系统声音?
很多笔记本厂商没有配置完整的声卡芯片驱动。这应该是录制驱动识别功能无法识别系统的声卡驱动的原因。对于台式电脑应该安装了提供这个功能的声卡,升级声卡驱动应该可以解决这个问题。
6、我怎样可以把PowerPoint录制为视频?
使用ALLCapture新建一个项目,然后在录制前选择分辨率,例如:800x600像素,打开PowerPoint开始录制,然后开始放映PowerPoint,并立即按下CTRL+SHIFT+P使PPT填充录制窗口,PPT播放完毕即可结束录制,然后剪掉前面的录制让第一页幻灯片的画面为起始页。
提示:如果幻灯片播放太快以至于没有捕捉到第一页ppt画面,你只需在ppt开始处插入空白的幻灯片,这样当播放时点击空白幻灯片后,真正的第一页幻灯片就可以录制到了。
未发布 【教程】Edraw Max(亿图图示):使用免费模板和示例快速制作发票? 外贸工作者长期与国外的用户打交道,除了需要用到英文或者其他语种进行沟通交流,还有一项也是不可或缺的技能,那就是制作英文版的发票。日常生活中,可能我们接触的国内的电子发票会比较多,比如日常吃饭、购物、停车等等,可是对于国外的发票很多人就会犯难了。
目前Edraw Max(亿图图示)在线订购享75折优惠活动正在进行中,欢迎您下载、购买进行运用!
通过亿图软件内置模板和例子快速创建
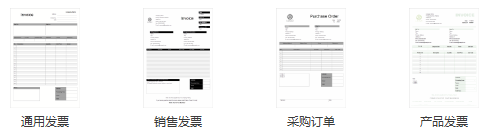
首先打开亿图软件,新建“表格”,然后在右侧模板中选择“发票”。如下图所示。
1、双击“发票“模板,即可快速创建一个空白绘图页面,左侧会自动打开相应的发票符号库。
2、从例子中选择所需发票实例,双击任意一个例子,即可调用该实例,然后就可以对其进行任意修改了。
发票的基本内容
1、公司详情,比如:公司名称、公司地址、公司电话和邮件地址,以及公司相关号码增值税注册号、发票号等等。
2、公司相关号码:增值税注册号、发票号。每张发票应该有一个独一无二的发票号。尽管被称作号码,它还是可以包含字母的,最常用的方法就是用发票前缀字母来表示客户,比如说ED001等。
3、客户详情:机构名称、客户姓名等等。
4、日期:日期中应该包含开具发票日期以及到期时间,在这个时间之前应该完成支付,一般为发票开具后的30天内。
5、服务和费用:这一项包含以下:服务描述、总金额、增值税数量和总量。
6、支付项目:是用来表示以何种方式获得这笔资金。
发票格式编辑
文件中所有元素都可以进行编辑,包括:表格宽度、高度和边框样式等。
合并或者分解表格:
只要你会用Excel,那么,用亿图只会让你的绘图效率翻倍,让你的工作效率加倍!
未发布 2017年8个最流行的Web编程趋势 互联网一直在不断的发展,这意味着开发人员必须及时了解当前的所有变化。人们在新闻、社交、购物到银行等各大方面都与互联网有着千丝万缕的联系。因此,为了满足全球数百万网络用户的需求,
Web开发需求正在上升。
Web编程趋势是在W开发的过程中不断变化,不断创新,并逐步淘汰已经过时的想法。以下是2017年你可能会看到的一些当前的Web编程趋势:
视频曾一度统治互联网,它能确保那些在线的人参与互动,并吸引受众停留更长的时间。随着网页上视频的观看次数显着增加,从长远来看,也可以带来更多的转化。
这是一个越来越多开发人员喜欢使用的集合。通过它,你可以创建单页应用程序,而不需要依赖于java中的框架。此外,该集合可以确保使用它的人做到最好。
这一直是一个趋势。开发人员正在使用Motion UI创建具有生命力的网站,并且还会对登录到其中的每个用户做出反应。这是出现在你屏幕上的特殊效果。
材料设计基本上是Google的一种哲学,它定义了应用程序在无线设备上的外观和性能。使用它可以更改所有类型,包括网站的风格和动画在布局中显示的方式。在视觉上,它正在成为开发人员的关键工具。
当你正在寻找创建在服务器上运行的网站时,你应该考虑这一点。这是一个趋势,因为它是创建网站的绝佳方式。创建的文件大大简化了,因为它们存储在除数据库之外的文件中。其拥有流量、安全性、速度和易于操作等优点。加载网站更容易、更安全。
浏览多个标签、以及链接到更多页面的网页已经是过去式了。现在用户正在选择单页面的网站、博客等类型。他们使用更方便,特别是在人们在旅途中的移动设备上。
Angular 2带来了很多转变,例如Google的JavaScript框架,这是完全重新设计的。它的好处是它利用了JavaScript ES6中的功能。这意味着未来的Web开发将变得更容易和有效。
这是未来Web开发中一个重要的趋势,特别是在游戏行业。它开始于Vive和Oculus Rift的到来,为游戏世界带来了巨大的可能性。像Google和Mozilla这样的全球性公司带来的API将有助于虚拟现实的转型。
Web开发人员必须了解Web编程的最新趋势,以便设计符合这些趋势的网站以及增加用户体验的网站。随着互联网的快速发展,这些趋势也会随之而变。因此,随时了解行业趋势是非常有用的。